Unicorns Legends and Mythology, and the relation to Cyberthreats.
In an opening paragraph by SAI360, “You’re never crossing paths with a unicorn: it’s the stuff of legends and mythology. Unfortunately, we can’t say the same about cyberthreats. Cyberthreats aren’t just real; they are inevitable.” I found some inspiration to read further “How to Respond to the 2023 Cyberthreat Landscape by Jeremy D’Hoinne, John Watts, et al.
I suggest the same… in my hole I found:
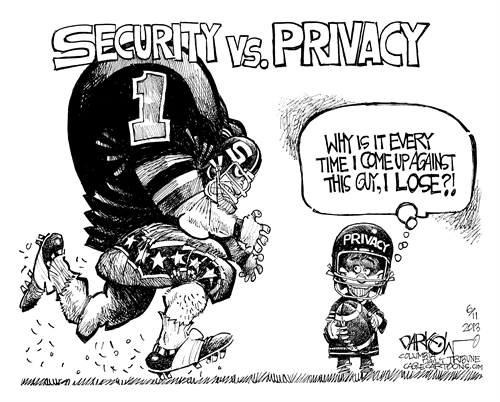
The ever-evolving threat landscape keeps security experts on their toes, just like the quest for unicorns. To navigate this digital wilderness, it’s crucial to understand the current micro-trends and recommendations in various areas of cybersecurity.
Threat Landscape Time Horizons Gap
One of the significant challenges in cybersecurity is dealing with threats that emerge at different time horizons. Some threats develop rapidly, while others evolve more gradually. Identifying this gap allows organizations to prioritize their security efforts accordingly. Invest in continuous threat intelligence gathering and real-time monitoring to bridge this gap effectively. Continuous monitoring, threat intelligence, and predictive analytics can help identify potential threats before they fully materialize.
Analysis of Malware-Ransomware
Malware and ransomware continue to be persistent threats, with attackers constantly adapting their tactics. Micro trends in this domain include the rise of file-less malware, which operates in memory and evades traditional detection methods. Recommendations include implementing endpoint security solutions, user training, and robust backup and recovery plans.
Evolving Phishing Tactics and Techniques
Phishing attacks remain a favored entry point for cyber criminals. Micro trends reveal the use of AI-generated phishing content and highly personalized attacks. Counter these threats with employee awareness programs, email filtering tools, and multi-factor authentication (MFA) for all email accounts.
Employee Account Takeover, Attacks Against MFA and Passwords
Account takeovers are on the rise, targeting both employee and customer accounts. Attackers exploit weak passwords and vulnerabilities in MFA systems. Combat these threats by enforcing strong password policies, utilizing adaptive authentication, and conducting regular security awareness training.
High-Momentum Threats, Customer Account Takeover
High-momentum threats, such as customer account takeovers, demand immediate attention. Micro trends suggest the use of social engineering tactics to gain access to customer accounts. To counter this, employ real-time fraud detection and educate customers about safe online practices.
Cloud Risks and API Abuse
As businesses migrate to the cloud, cloud-related threats are on the rise. Attackers target APIs to breach cloud environments. Micro trends indicate API abuse and misconfiguration. Secure your cloud infrastructure with robust access controls, encryption, and regular security assessments.
Targeted Attacks on Cyber-Physical Systems (CPS)
Attacks on Cyber-Physical Systems (CPS) pose severe risks to critical infrastructure. Micro trends reveal an increased focus on CPS vulnerabilities. Protect against these threats with network segmentation, anomaly detection, and penetration testing of CPS.
Uncertain Threats: Attackers Using AI
The use of AI by attackers introduces uncertainty into the threat landscape. Micro-trends include AI-generated phishing emails and automated vulnerability scanning reflecting that AI-powered attacks are becoming more sophisticated. Defenders must employ AI for threat detection, anomaly detection, and automated incident response.
Non-technology Threats
Cybersecurity is not just about technology; it also involves human and organizational elements. Employee activism is a growing concern, with insider threats and leaks becoming more frequent. Micro-trends include hacktivism and whistle blowing. To address this, organizations should foster a culture of transparency and provide channels for employees to voice concerns.
Conclusion
The cybersecurity landscape is a dynamic and ever-changing field where the unexpected can occur at any time. By staying informed about micro trends, we can better prepare ourselves to confront both known threats and those that may emerge.
Just as the search for unicorns continues to capture our imagination, the quest for absolute cybersecurity may remain elusive. However, by staying informed about the evolving threat landscape and implementing the recommended micro-trends, organizations can significantly enhance their defenses. In the ever-changing world of cybersecurity, being prepared is the closest thing we have to a unicorn: a rare and precious asset.
Remember, the key to a resilient cybersecurity strategy is adaptability, continuous learning, and proactive measures to safeguard your digital assets against all potential adversaries, whether they be human or mythical.
…and now back to Harry Potter.