Why Agile Risk Governance Is No Longer Optional in 2025
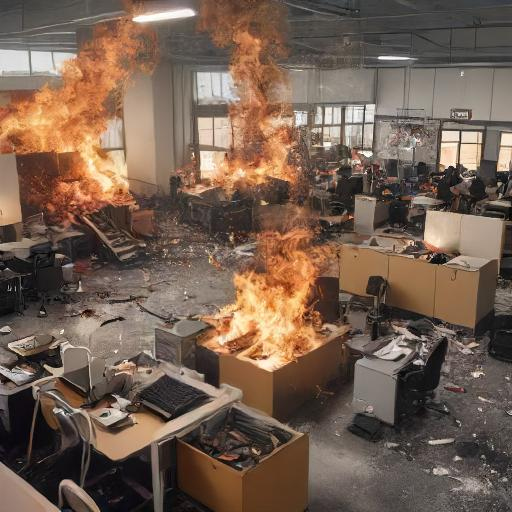
Your governance model might be your biggest vulnerability — or your greatest strategic advantage.
In a world where threats emerge overnight and ripple across borders in hours — cyberattacks, extreme weather, political unrest, supply chain failures — traditional governance models are falling behind.
By the time a quarterly board review rolls around, the damage is often done.
That’s why in 2025, the organisations that are thriving aren’t just the ones managing risk — they’re the ones rethinking how governance works altogether.
Governance for Speed, Not Just Control
Most governance structures were built for compliance, policy, and oversight. While still important, that model can’t keep up with:
- Real-time cyberattacks and ransomware threats
- Sudden regulatory shifts on AI, data privacy, ESG, and supply chains
- Fast-moving disinformation or reputational crises
In 2025, decision speed is risk management. Waiting to escalate issues through long hierarchies or outdated processes puts your organisation at a disadvantage — or worse, at risk of irreversible harm.
What Agile Risk Governance Looks Like
Think of it as a shift from slow “check-the-box” oversight to real-time situational awareness and cross-functional response.
Here’s what defines agile risk governance:
Continuous, dynamic risk intelligence
Boards and leadership need current, not quarterly insights. Dashboards, predictive analytics, and cross-departmental reporting can provide early warning signals and trend mapping before threats escalate.
Cross-functional coordination
Risk no longer lives neatly in one department. Legal, IT, HR, operations, ESG, security — all need shared visibility and fast alignment when new risks emerge.
Decentralised decision authority
Front line teams and middle management often see risks first. Agile governance empowers the right people to act fast — with clear escalation paths and accountability structures.
Transparent, traceable decision-making
Responsiveness doesn’t mean recklessness. Agile governance ensures decisions are made quickly but documented clearly, with regulatory expectations and ethical considerations built into the process.
Why This Matters to Everyone — Not Just the Board
Agile risk governance isn’t just a C-suite problem. It creates a culture where everyone is empowered to spot and speak up about risk — and where those signals are actually heard and acted on.
For everyday professionals, this means:
- Understanding how your role connects to risk decisions;
- Having clear, fast channels to report concerns or disruptions;
- Knowing your organisation takes speed and transparency seriously — not just post-crisis
Questions to Help Your Organisation Become More Agile
Ask these within your team or leadership circles:
- Can we detect and respond to new risks within hours — not weeks?
- Are risk insights shared across silos, or trapped in one department?
- Do our decision-makers have the data they need to act fast — and ethically?
- Do we regularly test our response to emerging threats?
If the answer to any of these is “not yet” — that’s your starting point.
In 2025, Responsiveness = Resilience
Agile governance isn’t just about reacting fast — it’s about building a living system of oversight and action that evolves with the world around it.
As the pace of disruption accelerates, rigid governance becomes a liability.
But agile risk governance? That’s your new strategic edge.
It’s not just about protecting the organisation — it’s about making it ready.