Unveiling the Hidden Threat: Safeguarding Your Enterprise through Vigilant Employee Off boarding
In the intricate dance of corporate security and the human psyche, the act of off boarding an employee, whether voluntary or involuntary, bears the potential to unmask insidious threats that may otherwise remain concealed. The routine may seem innocuous—devices surrendered, imaging and archiving executed—but lurking beneath the surface lies a perilous chasm of unexplored vulnerabilities. It’s time to venture beyond the mundane and delve into the uncharted territories of computer activity preceding an employee’s departure. The question echoes: Are you truly prepared?
In this relentless pursuit of safeguarding your enterprise, distance holds no dominion. Even amidst a landscape dominated by remote work, the relentless march of technology-driven espionage threatens to breach the ramparts of your digital fortress. Prepare to traverse the labyrinthine pathways of data exfiltration and the menacing specter of intellectual property theft. Brace yourself for revelations that will shatter preconceptions and empower your security arsenal.
Unmasking the Invisible: Strategies for Detecting Data Exfiltration and IP Theft
- Probing the Web of Intrigue: As the electronic tendrils of your corporate network pulse with life, vigilance becomes paramount. Elevated network activity, manifesting as torrents of downloads and uploads, must not escape scrutiny. Within this maelstrom of data flux, shadows of malevolent intent often lurk, waiting to be exposed by your relentless vigil.
- Eyes on the Unseen: Peering into the digital footprints of departing employees can yield unparalleled insights. Gaze upon the applications they dared to invoke, their journey through the virtual realm, and most crucially, their interaction with the sanctum of confidential network shares. It is in these whispered interactions that the secrets of their intent are whispered, ready to be deciphered by the discerning guardian.
- Whispers of Betrayal: The tendrils of threat extend beyond the confines of the terminal. Did an external storage device, a modern-day Trojan Horse, ever breach the citadel? Unmask the machinations of covert data pilferage as you trace the sinister journey of these concealed conduits, poised to siphon the lifeblood of your enterprise.
- The Cartography of Intent: Pinpointing the locus of activity transcends mere geography—it is the very essence of understanding the psyche at play. Unearth the places whence the actions of departing employees emanate: the familiar refuge of home, the battlefront of the office, or the enigmatic crossroads of public WiFi. Within these coordinates, motivations crystallize and vulnerabilities fester.
The marriage of security and psychology casts an indomitable shield around your fortress. The routine, no longer a shelter for complacency, transforms into a battlefield where resilience prevails. The solemn duty of off boarding now embraces the mantle of a sentinel, deciphering whispers of treachery and decoding the enigma of intent.
In this labyrinth of departure lies an opportunity—an opportunity to rise above the ordinary, to transcend the conventional. The sentinel, armed with knowledge, unearths the hidden currents that betray the harmony of the enterprise. As the embers of departure fade, let them illuminate a path to security unyielding and resilience unparalleled. Stand vigilant, for in the crucible of off boarding, the future of your enterprise is both forged and safeguarded.
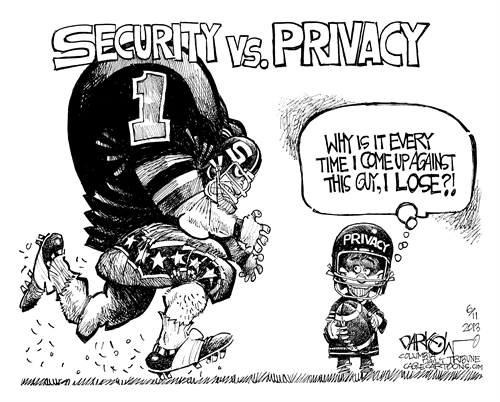
And then… does it conflict with their privacy?